Last summer, Equifax was hacked. The consumer credit agency lost control of data that included the social security numbers, dates of birth, driver’s license numbers and other personal information of more than 140 million people in the U.S., and hundreds of thousands more in Canada and the U.K. If you were interested in stealing someone’s identity, this is precisely the information you’d want. With this one breach, Equifax, whose very reason for being is to protect consumers against fraud, turned from a business creating value to one that had destroyed it.
Companies get hacked all the time. And most large organizations take measures to protect their data. The sheer number of records that were stolen from Equifax suggests that the company may have been lax about data security. But no system is foolproof. Breaches will occur, and the key is knowing what to do afterward.
Rotman faculty members who study business strategy recently published Survive and Thrive, which explains how the best companies handle existential risks to their businesses. In the book, we caution against the “ostrich effect” – ignoring threats and hoping they don’t occur on your watch. But we also look at situations in which firms have successfully managed threats. And one of the best techniques is what we call “structured anticipation.”
There are two key points to be made. First, companies should always have a Plan B. They should work through scenarios – in the case of Equifax, a breach of security and loss of information control – and ensure that they’ll learn about these incidents in a timely manner. At the same time, they should have a process for when such incidents arise, and ensure that employees are aware of it. Every airline pilot has a manual to cover every imagined contingency. The same is needed for organizations – especially with regard to their greatest risks. For Equifax this would have meant appointing the right person to manage the crisis, establishing a clear line of reporting between this person and senior management, and relying on a set of procedures for communicating to customers about the breach.
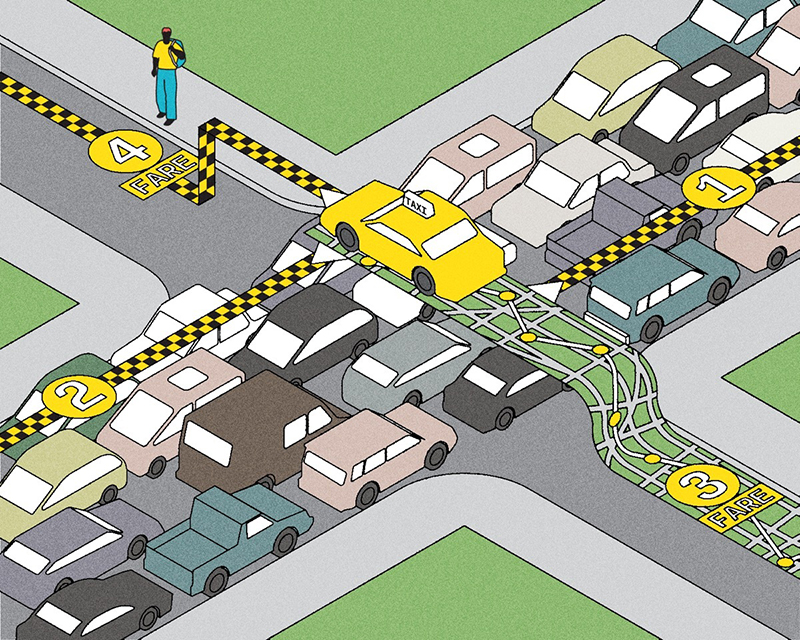
We know now that Equifax – if it had planned for this at all – had not put a set of procedures in place. For a start, it waited more than two months to inform customers of the breach. While it’s probably not wise to go public immediately (false alarms could be just as bad), Equifax seemed to drag its feet. When the company finally did announce the problem, it set up a completely separate website for consumers to reenter their personal information before they could gain access to remedial action. The website was designed so poorly that it could have been mistaken for one of the fake sites that were set up by spammers hoping to capitalize on the breach. Equifax’s own Twitter account even directed users to one of the fake sites! Clearly, the company had not thought this through.
The second important point is for companies to foster a culture that encourages dissent. If an IT person within Equifax knew of a vulnerability, it appears he or she didn’t bring this to the attention of the C-Suite. Indeed, the delay may have arisen precisely because no one wanted to be the messenger with bad news. That suggests a culture that punishes messengers – something that makes a disaster such as Equifax’s all the more likely.
As a rule, managers get into trouble when they avoid managing. Managers who are averse to the consequences of a backlash will often look for solutions that primarily insulate themselves from blame. By contrast, the best managers see the world – and their own systems – as imperfect, and they establish protocols so that they and others can manage fires as soon as they arise. Whatever else Equifax may have done, one thing they did not do is manage the crisis. When Plan A failed, they had no contingency. Not surprisingly, the outcome turned out to be “early retirement.”
Joshua S. Gans is a professor of strategic management at the Rotman School of Management and co-editor of Survive and Thrive: Winning Against Strategic Threats to Your Business.
Recent Posts
People Worry That AI Will Replace Workers. But It Could Make Some More Productive
These scholars say artificial intelligence could help reduce income inequality
A Sentinel for Global Health
AI is promising a better – and faster – way to monitor the world for emerging medical threats
The Age of Deception
AI is generating a disinformation arms race. The window to stop it may be closing